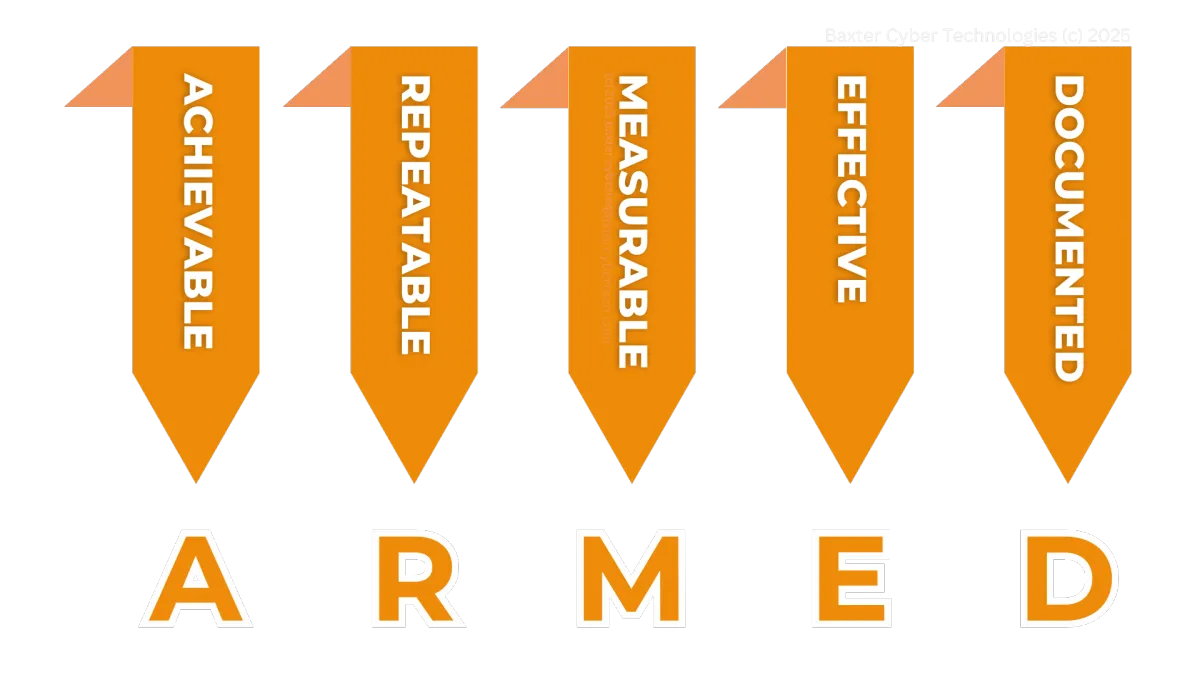
The ARMED Cybersecurity Framework
Simple, not easy.
Information Security Programs are usually where good intentions go to die. Nobody reads them, nobody follows them, nobody updates them, and most of all, nobody cares. Unless carefully constructed, they become paper tigers without impact.
Auditors regularly see programs with pie in the sky ideals but no real traction in the real world. Requirements to change passwords every thirty days but no technical controls that enforce it and no evidence to prove it.
No silver bullets. No easy buttons. Vague generalizations won't cut it. Hope is not a good business strategy.
Is your Information Security Program ARMED for sustainable compliance?

Achievable
Every requirement of a compliance standard asks a question. Those questions require an answer, if if the answer is no or nothing. To be achievable, an Information Security Program cannot require of itself impossible standards.
For instance, it cannot prove zero unauthorized access attempts past, present or future. It can, however, demonstrate evidence of an unbroken string of required periodic password changes by date and by user.
Repeatable
Your Information Security Program cannot exist in flurries of ad hoc activity. It cannot be done differently every time. Even if you avoid violations, it only happened by good luck and random chance. It cannot be sustained.
Every compliance activity must be easily repeatable. In fact, it should be the most straight forward way to get the job done. Busy people generally follow the path of least resistance, so the program should set your security controls and compliance artifact creation to be almost automatic.


Measureable
Compliance activity makes comparisons. The state before and the state after matter. What are the differences, if any? The system software needed a security patch and then the security patch was applied. Some defined aspect of your system changed.
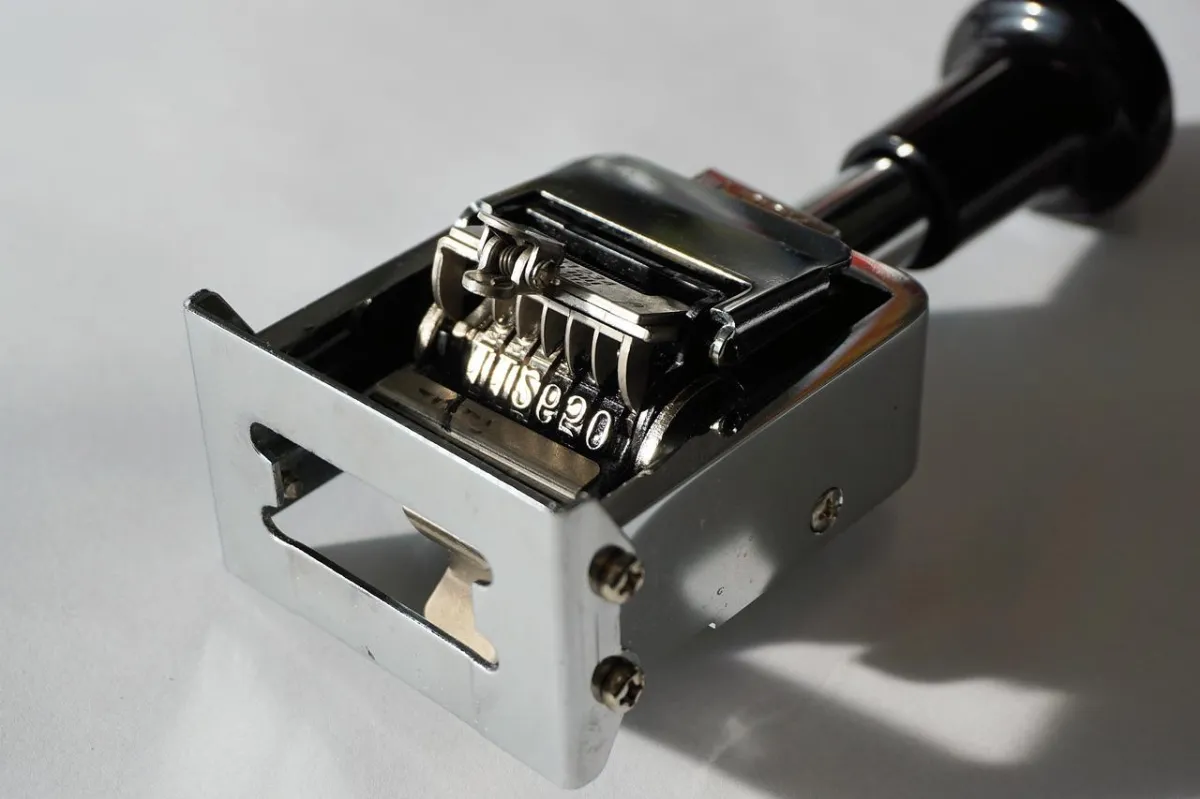
Measurable activity, then, takes place at a specific point-in-time. An Information Security Program can point to it, touch it, time it, or scan it. Everything in the program, every choice, decision, and activity must produce an artifact. Some tiny piece of data that proves the exercise of the process.
Effective
If nothing changes, then nothing changed. Information Security Programs cannot fill our days with useless activity. Good compliance does not just mean busy people, but effective and efficient people who keep a business compliant without great amount of extra effort. Maybe not any.
A convoluted and complex compliance program will fail. Count on it. People do not like spinning their wheels on extra steps that bring no profit into the company. If they can't see it work, they won't do it. At least, not long-term. It really doesn't matter how threatening the policy language sounds.

Documented
Every step of the way, a good Information Security Program records evidence. An artifact of compliance proves who followed the process, when they did it, and what they did. As every auditor will tell you, if it isn't documented it didn't happen.
Compliance is the "game" of demonstrating evidence. The policy document alone won't matter if no evidence exists to sample in an audit. If the auditor asks what happened the second Tuesday of last April, what evidence can your program produce? Even if you can nothing whatsoever happened on the sampled date, you still have to demonstrate that from your recorded artifacts.
Does your Information Security Program have Achievable, Repeatable, and Measurable goals? Is it Effective? Is it Documented? It could be! Start on the journey to better cybersecurity and compliance today. We would love to help.
Does your ISP contain these best-practice elements?
Information Security Programs work at five distinct levels. Each has its own work to do. Companies often write policies that sit forgotten on a drive share without any real power. Even if they include disciplinary measures, those cannot be exercised without great risk of litigation, since the company cannot demonstrate personnel following the policies consistently. Better no policy at all than a policy only followed occasionally.
Policy provides only one building block of a strong program. Mapped processes, accurate context-based procedures, and organized evidence of practice outweigh any dozen dusty documents!

Why not start with a proven Fixion Program Template?
Writing Information Security Programs can be difficult and time-consuming. Start with a program derived from thirty-years of experience both in auditing and being audited. Most cybersecurity professionals can't say they ever sat on both sides of the table, over hundreds of audits, with multi-million dollar fines on the line!
Each of the five elements of the Baxter Fixion Program follows the ARMED framework to the letter. This complete program easily be adapted to PCI-DSS, HIPPA, SOX, or any other type of cybersecurity regulation or requirement.
The Fixion Program not only includes templates, but also organization and retention tools, and many hours of detailed video training. These resources assist busy professionals like yourself implement an effective ISP without negatively impacting business.
It all starts with your first free discovery consultation.